Importance of Data Protection in the Cloud
As technology continues to evolve and organizations are adapting to Cloud computing on an ongoing basis, threats continue to grow in sophistication and in complexity. Cyber security and data protection continue to be a key focus for business leaders and key regulators across the globe, as a range of risks, vulnerabilities and emerging trends affect their approach to enhancing their digital safeguards in 2022. Protecting the data on premises or on cloud has always been a big challenge, but the rate of risk is accelerating and evolving day by day across the globe. Access to data is extremely crucial in the cloud and data loss has become an emerging risk in the current threat landscape.
Some of the Key Challenges of protecting the data in Cloud –
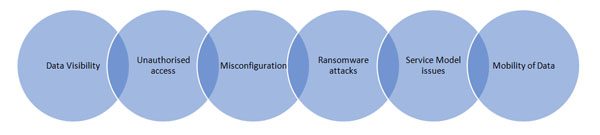
In the cloud environment, it becomes serious on protecting the data as the data is located in different places across the globe. With the Digital revolution across various industries small or large are relying on operating systems and thus making cyber security a primary goal to safeguard data from various cyber-attacks or ransom ware attacks. With so many policies to impose and applications to keep up to date, organizations are facing key challenges in aligning to ISO standards and industry best practices.
The number of applications migrating to cloud across various industries has been growing consistently since cloud platforms support enterprises with a more secure channel for storing their content, applications, and data. For moving to cloud, all organizations are required to have a robust cloud security posture to be imperative. With security threats regularly developing into more sophisticated structures, cloud security is no less at risk than an on-premises ecosystem. Lack of control over the data and misconfigurations have been key threats in the cloud atmosphere. Protecting the data from internal / external threats are vital and critical to business
Here are the top emerging risks in data security on cloud –
- Ransomware attacks
- Rise of Data Security Breaches
- Increase in Data privacy regulations
- Potential of growth in Artificial Intelligence
- Mobile is the New Target
- Evolving vulnerabilities in Cloud
- Supply Chain attacks are on the Rise
- Automation arising in the cloud platform
- Insider threats
As the technology landscape keeps evolving, organizations are facing tremendous pressure to secure their corporate data and ensure they meet business requirements. Managing data in cloud is highly critical to safeguard the critical data and business reputation of an organization. A holistic approach to navigate the ambiguity and handle the complications arising in the business environment is the growing challenge in the current industry trends. Defending against modern cyber threat campaigns requires the ability to respond quickly and correctly to rapidly evolving attacks that can strike anywhere within an organization’s IT infrastructure.
In the absence of standard practices or mechanisms, organizations may take different measures to ensure protection of Data Security and Privacy. Ensuring data protection and security measures is a continuous journey which needs attention of organizations for taking proactive measures to safeguard the data from emerging threats.
Some of the benefits in having the data in Cloud –

Emerging risks and vulnerabilities have revealed that the implementation of data security controls is significantly important based on the rate of technology growth across the countries.
Some of the global Best Practices to overcome the data loss:
- Develop employee awareness culture within the DNA of the organization
- Enable restricted access for all employees and implement MFA (Multi-Factor Authentication) to ensure multi-layer security.
- Create a data usage policy.
- Establishing a process for the backup and recovery of essential data.
- Install anti-virus software and keep all computer software patched on an ongoing basis.
- Update operating systems, applications, and antivirus software regularly.
- Reduce 3rd party / supplier dependencies
- Disable pop-ups, unknown emails, and links to avoid Phishing / Social Engineering.
- Use Data Encryption.
- Use endpoint security systems to protect your data.
- Conduct an Annual Penetration test and Vulnerability assessment.
The objective of data security planning and controlling in the cloud is to minimize the risk of data loss and safeguard the data across the organization. Data security is an ongoing process that needs to be understood, adapted and align to industry best standards to stay resilient in nature. Organizations should continuously adapt to the changing needs in processes, regulations and methods with the technology and constantly evolve as per the growing threats and emerging trends.
About the Author :

Ms. Kavitha Srinivasulu
Global Head – Cyber Risk & Data Privacy – BFSI R&C
Tata Consultancy Services
Ms. Kavitha Srinivasulu has around 19+ years of experience focused on Cybersecurity, Data Privacy & Business Resilience across BFSI, Financial services, Retail, Manufacturing, Health care, IT Services and Telecom domains. She has demonstrated her core expertise in Risk Advisory, Business Consulting and Delivery assurance with diverse experience across corporate and Strategic Partners.She is a natural leader with versatility to negotiate and influence at all levels.
The views and opinions expressed by Kavitha in this article are only from her personal side and not representing her company viewpoints or sharing any of her customers views.
Ms. Kavitha Srinivasulu is Bestowed with the following Licenses & Certifications :
https://www.linkedin.com/in/ka
https://www.linkedin.com/in/ka
Ms. Kavitha Srinivasulu can be contacted at :
LinkedIn : https://www.linkedin.com/in/ka
Also read Ms. Kavitha’s earlier article: